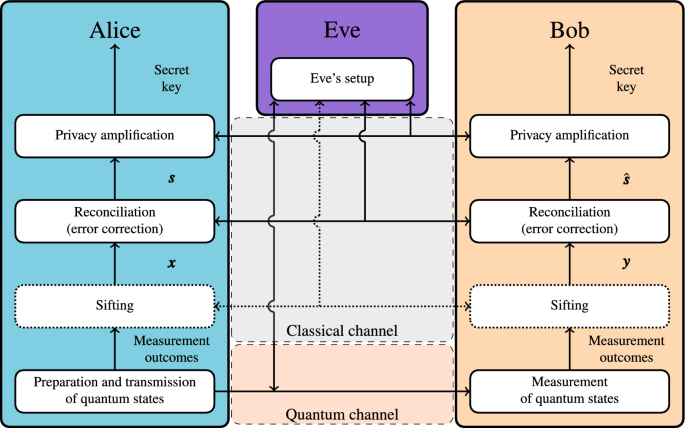
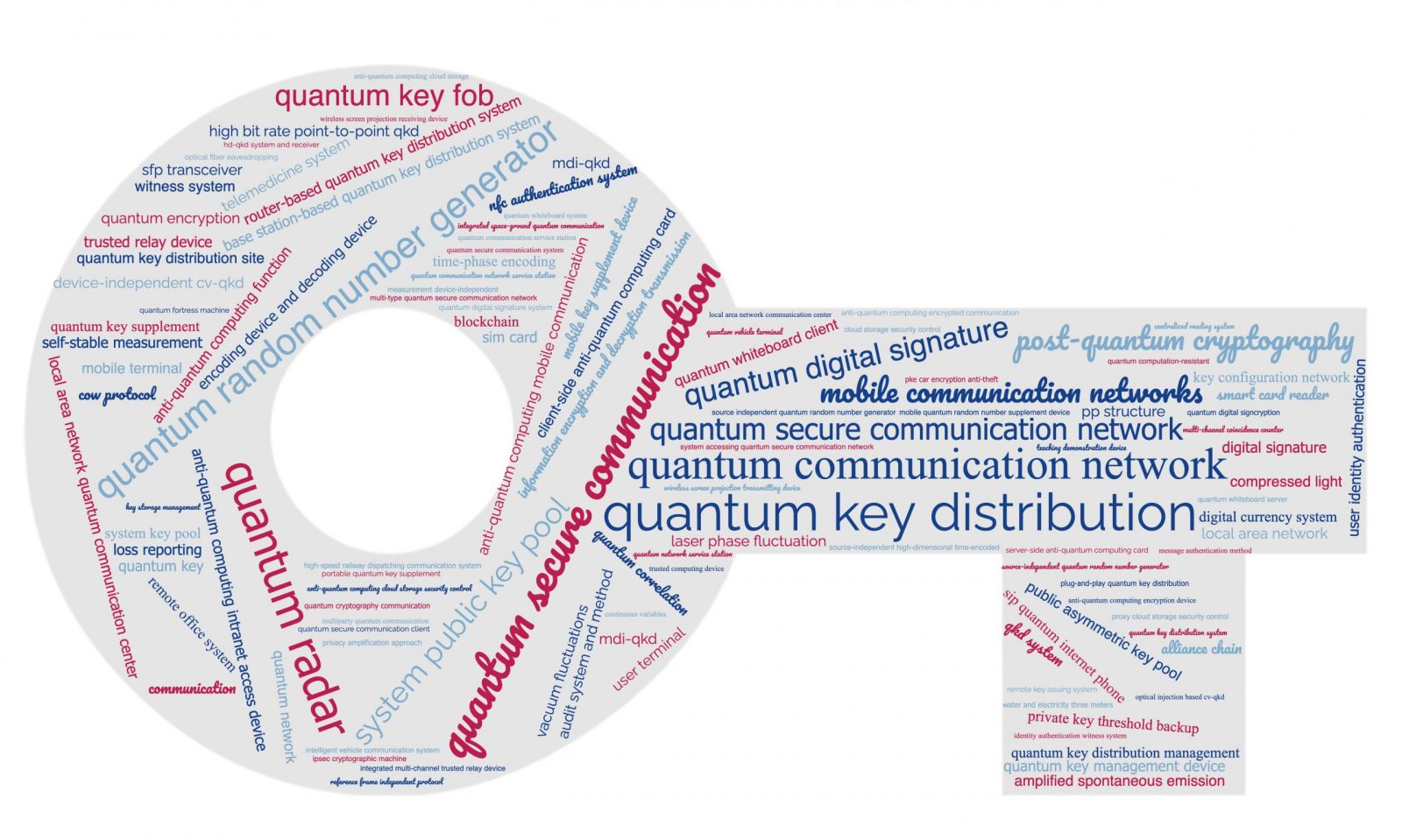
High-speed and Large-scale Privacy Amplification Scheme for Quantum Key Distribution | Scientific Reports
![PDF] High-Speed Implementation of Length-Compatible Privacy Amplification in Continuous-Variable Quantum Key Distribution | Semantic Scholar PDF] High-Speed Implementation of Length-Compatible Privacy Amplification in Continuous-Variable Quantum Key Distribution | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/ae99d388ed29641fe1f2ad079011469e2fce1f87/5-Figure1-1.png)
PDF] High-Speed Implementation of Length-Compatible Privacy Amplification in Continuous-Variable Quantum Key Distribution | Semantic Scholar
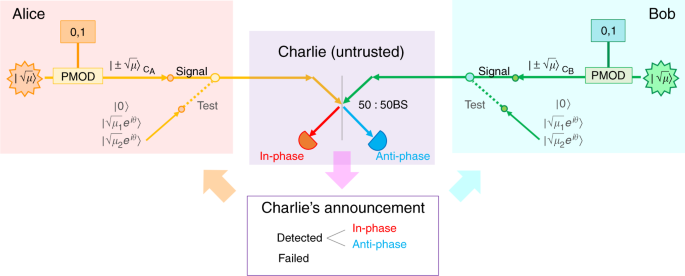
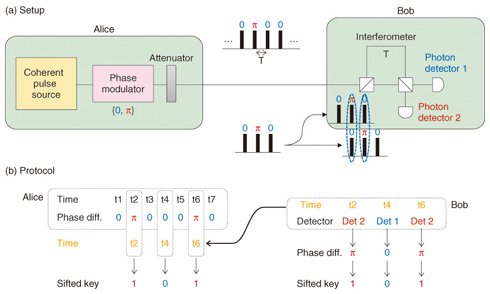
Entropy | Free Full-Text | An Improved Slice Reconciliation Protocol for Continuous-Variable Quantum Key Distribution
A novel error correction protocol for continuous variable quantum key distribution | Scientific Reports
![PDF] High-Speed Privacy Amplification Scheme Using GMP in Quantum Key Distribution | Semantic Scholar PDF] High-Speed Privacy Amplification Scheme Using GMP in Quantum Key Distribution | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/5ab3cb538f80f4bbf539103464fe597ba2d93a7c/2-Figure2-1.png)
PDF] High-Speed Privacy Amplification Scheme Using GMP in Quantum Key Distribution | Semantic Scholar
![PDF] High-speed Implementation of FFT-based Privacy Amplification on FPGA in Quantum Key Distribution. | Semantic Scholar PDF] High-speed Implementation of FFT-based Privacy Amplification on FPGA in Quantum Key Distribution. | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/00d9158399761b85815dfddbff75a1e12d55017c/3-Figure1-1.png)
PDF] High-speed Implementation of FFT-based Privacy Amplification on FPGA in Quantum Key Distribution. | Semantic Scholar

PDF) A QKD Protocol Extendable to Support Entanglement and Reduce Unauthorized Information Gain by Randomizing the Bases Lists with Key Values and Invalidate Explicit Privacy Amplification | Naveen Srinivasan - Academia.edu
QKD as the Most Likely Quantum Technology to be Adopted in the Short-Term - Inside Quantum Technology

The procedure of accelerating length-compatible privacy amplification... | Download Scientific Diagram

The process of length-compatible privacy amplification algorithm. The... | Download Scientific Diagram

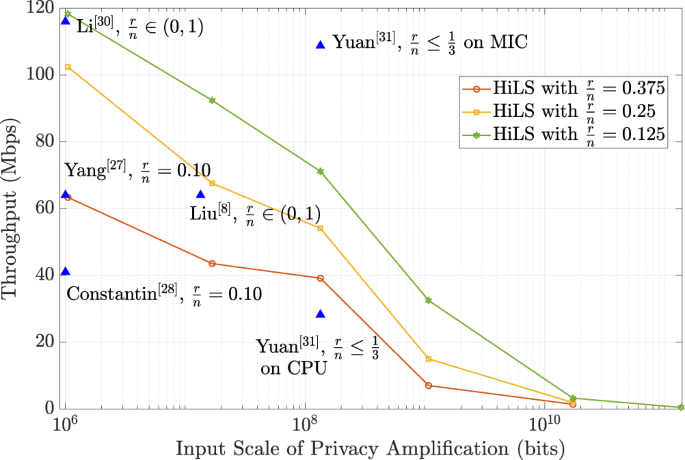
High-speed and Large-scale Privacy Amplification Scheme for Quantum Key Distribution | Scientific Reports
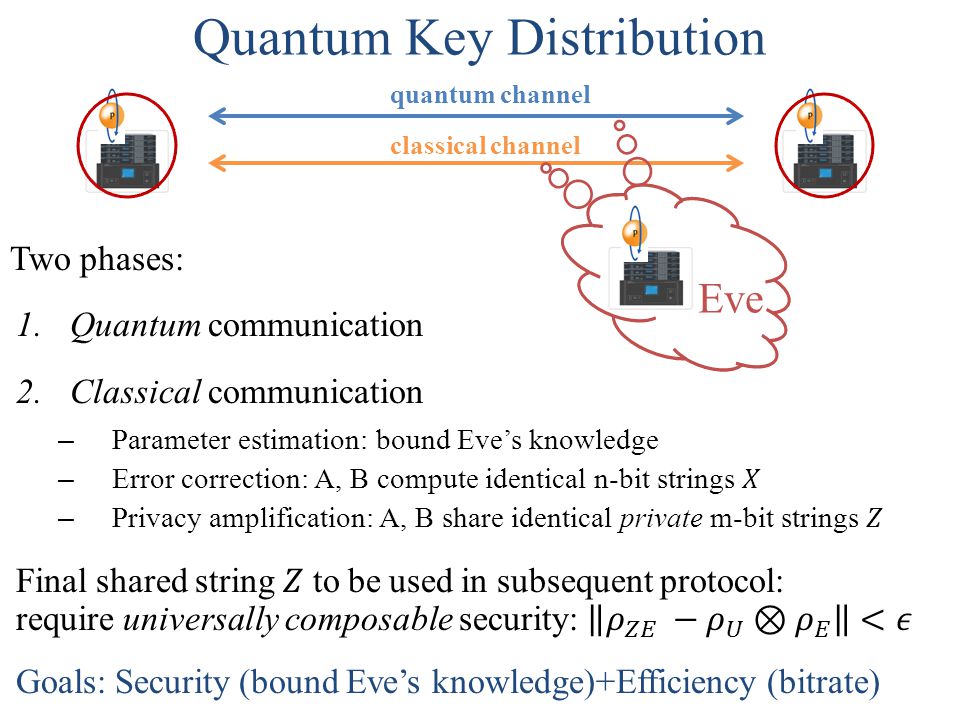
Randomness Extraction and Privacy Amplification with quantum eavesdroppers Thomas Vidick UC Berkeley Based on joint work with Christopher Portmann, Anindya. - ppt download
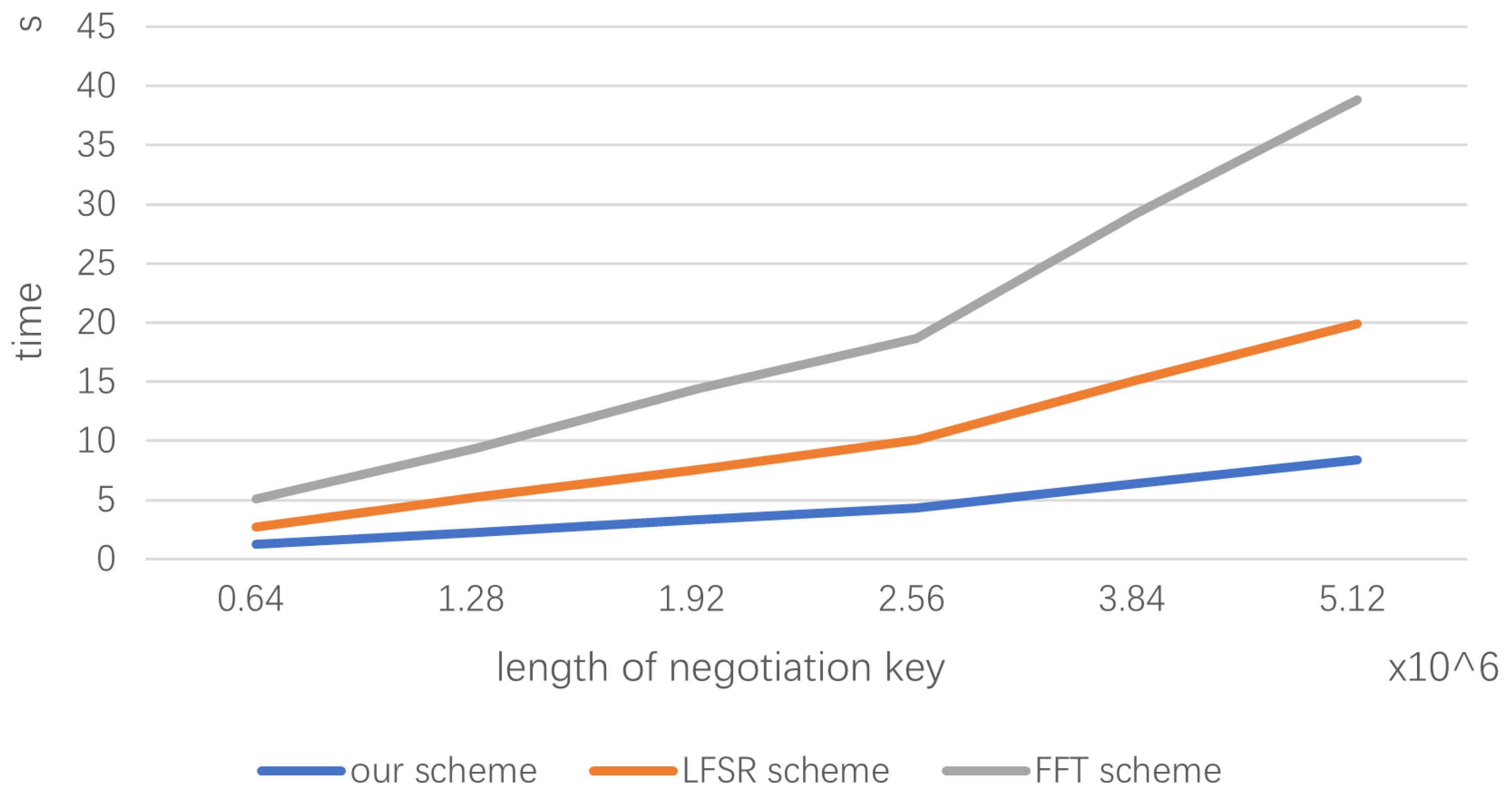
Electronics | Free Full-Text | High-Speed Privacy Amplification Algorithm Using Cellular Automate in Quantum Key Distribution
![PDF] High-Speed Privacy Amplification Scheme Using GMP in Quantum Key Distribution | Semantic Scholar PDF] High-Speed Privacy Amplification Scheme Using GMP in Quantum Key Distribution | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/5ab3cb538f80f4bbf539103464fe597ba2d93a7c/1-Figure1-1.png)
PDF] High-Speed Privacy Amplification Scheme Using GMP in Quantum Key Distribution | Semantic Scholar
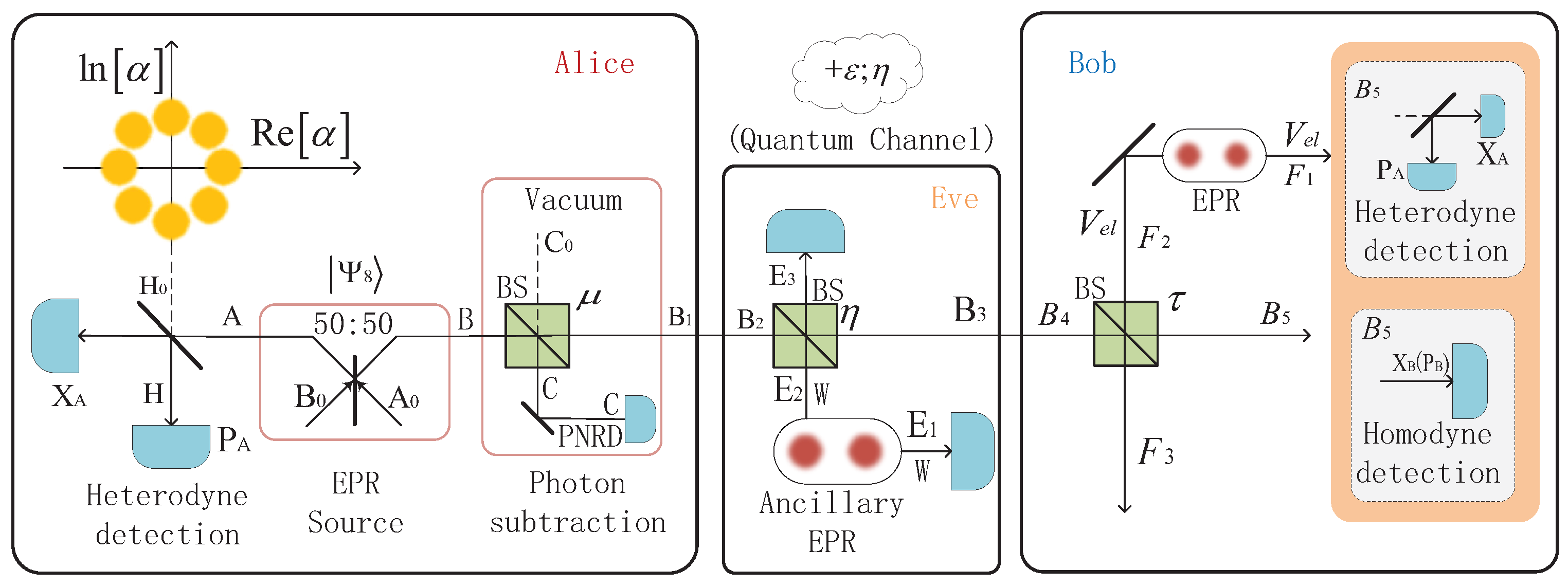
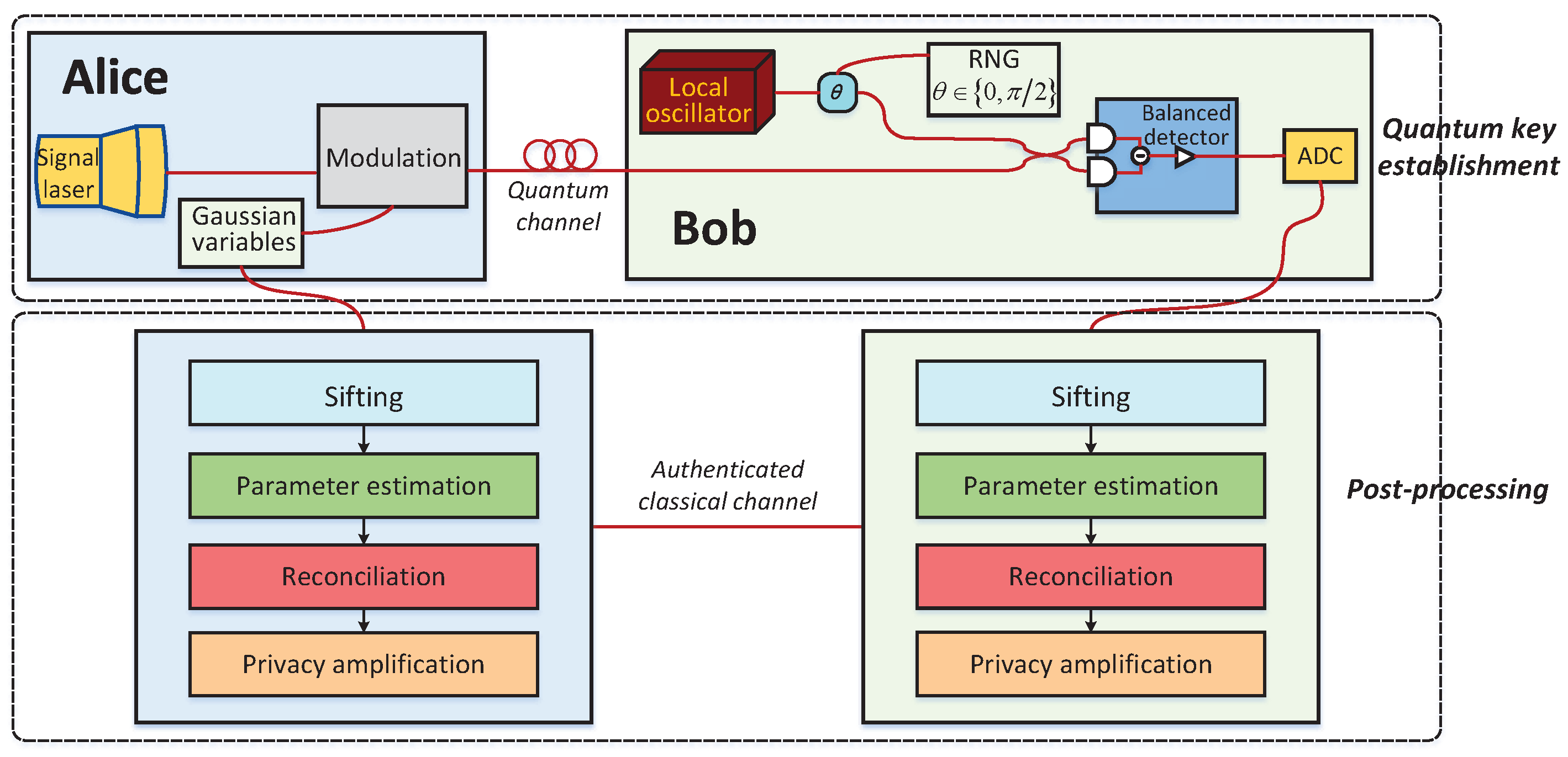
Applied Sciences | Free Full-Text | Improving Eight-State Continuous Variable Quantum Key Distribution by Applying Photon Subtraction